How to Design and Create a Secure Website
We recently wrote about the dangers of data breaches and the financial impact they have. But are you really making sure your websites are secure from the latest threats? Web applications are an increasingly important part of the online ecosystem, but if you’re not familiar with the latest vulnerabilities then everything you touch could wreck serious havoc.

“Under Construction” (CC BY-SA 2.0) by Eric Kilby
Just as you need to consider the user experience for your latest web design, security should also be a key consideration. Ensuring that each piece of your virtual puzzle is locked in tight and secure should, in reality, be your main priority. Indeed, a website that looks great but puts it’s visitors in danger causes more harm than good.
With this in mind, we’ve compiled an overview of what web application security protects you from, how you should fight it and, finally, why you should be protecting yourself.
What Are Web Application Attacks?
When it comes to defining web application attacks, Incapsula has broken down the most common threats. Working from the idea that web application security is the process of protecting websites from “vulnerabilities in an application’s code.”

“Hacker” (CC BY 2.0) by Visual Content
Incapsula outlines four types of attacks you need to be aware of:
- SQL Injection – After exploiting an SQL weakness to allow malicious queries to be sent to the database, attackers can then extract sensitive information from an infected system.
- Cross-site Scripting (XSS) – Either reflected or stored, XSS attacks are a form of injection that infects users who access or download an infected application.
- Remote File Inclusion – After remotely injecting a file onto a web application server, a hacker can execute malicious scripts or code within the application and, potentially, steal sensitive data.
- Cross-site Request Forgery (CSRF) – This exploit causes an infected browser to perform an unwanted action in a site. This can then be used to steal funds and/or personal information from the site where the user is logged in.
The Developer’s Security Checklist
Education is the first step in securing your websites, but simply learning the details of web application security and the major threats isn’t enough. Regardless of whether you’re a novice developer or a seasoned pro, there are certain areas you need to address both in the design and testing phase of a website.
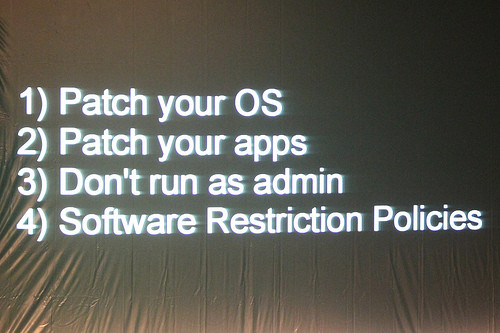
“The 4 most essential rules” (CC BY-SA 2.0) by 4nitsirk

For help in this area, the SANS Institute has compiled a handy security checklist. Although it’s intended for IT professionals who are not programmers, the 11-point plan should serve as an important reminder for those involved in the coding process.
According to SANS, the following points need to be addressed when attempting to secure web applications from malicious and unintentional abuse:
- Risk Assessment – which areas of the application are most at risk and, therefore, most in need of securing?
- Authentication – the first line of defensive, authentication procedures should include password expiry times, automatic account lockout on failed attempts, suitable password recovery and more.
- Authorization and Access Control – websites should have appropriate levels of access with end users typically be set to the lowest level or “least privilege.”
- Session Management – a common vulnerability here is not protecting session tokens. To address the issues, encrypting sessions and randomly assigning session IDs should be implemented as a minimum precaution.
- Data and Input Validation – to protect against XSS, a developer must ensure the server is able to validate an input against known good criteria.
- Command Injection Flaws – to ensure your web application doesn’t have an open door for malicious code to be pushed through, all parameters must be examined for calls to external sources.
- Buffer Overflows – an application that’s flooded with data can be compromised. To ensure this doesn’t happen, make sure any code that accepts data from an HTTP request is capable of reviewing large quantities before dropping it.
- Error Handling – have a written document with a clear strategy for error handling to avoid any problems leading to a possible weakness.
- Logging – time and date stamps should always be accurate. Synchronize servers and syslog servers to a time server.
- Remote Administration – try to limit remote administration where possible.
- Web Application and Server Configuration – make sure that all servers are customized and patched where necessary to meet the client’s demands.
Why You Need to Be Serious About Security
Why is this so important? On one level, an insecure web application could cost you financially – a 2015 IBM report suggests the average cost per lost record is $158. If an oversight on your part leads to a data breach, you could be liable for the damages. But the implications can reach further than that. Let’s look at a couple of examples.
“Computer Security – Padlock” (CC BY-SA 2.0) by perspec_photo88
Firstly, search engine giant Yahoo! have only just realised that they became the victim of what has been widely dubbed as ‘the biggest hack in history’ back in 2014. A colossal 500million accounts were breached and it has now led to a $4.83billion takeover deal with telecommunications firm Verizon to be called into question.
You also might want to consider using a VPN service to make sure you’re protected.
But, the implications of poor security can transcend issues relating to business and money. Look at the hack of the extramarital dating site Ashley Madison – the website that people logged onto in order to cheat on their spouses. People lost their lives as a direct result of this cyberattack, one of the most devastating in the internet’s history. At least two people committed suicide after the hack because they couldn’t come to terms with their online actions, according to the BBC, and countless divorces were observed. These are all situations that could have been avoided if the company had taken online security seriously.
